Drilling Contractors should consider engineered cybersecurity approach
By Alex Endress, Editorial Coordinator
As companies consider how to defend against cyber threats in the digital age, many will take an IT approach. This means prioritizing the implementation of firewalls and antivirus software. However, for drilling rigs, these tools will not be sufficient to ensure cybersecurity. Mike Van Gemert, Senior VP of Northwest Technical Solutions, urges drilling companies to consider an engineering approach, which requires a deep understanding of the physical, logical and operational components of a drilling rig. “Until you understand the systems, you usually can’t grasp the risk,” he said. “They are connected.”
By understanding at a detailed level how various systems on a rig are interconnected, offshore drilling contractors will gain a better picture of their cybersecurity risks, Mr Van Gemert said. The engineering approach takes into account how modern internet-connected drilling equipment is physically linked to the rig’s data network, how the rig’s data is logically configured and the efficacy of an organization’s operational protocols regarding cybersecurity. “You need to finitely understand where the risk sits, how it propagates and how it comes onboard,” he said.
Without this sort of understanding, drilling contractors may be leaving rigs open to threats that the companies may not even know exist. Through his experiences inspecting rigs in the Gulf of Mexico, Mr Van Gemert said: “There’s not been one vessel that we have been on that we have not found a cyber-related risk of some sort be that physical, risk – due to physical access and at risk architectures. Logical – systems and logic that are particularly prone to cyber risk due to malware or Trojan threats and operational – where rigs and organizations lack awareness of the true risks and governance to ensure proper cyber risk management. We have observed such impact on all vessel systems.
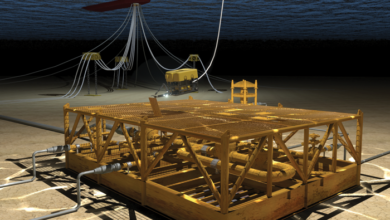
The physical concept within Mr Van Gemert’s engineering strategy means drilling contractors should understand the architecture of a rig’s network. That understanding would allow them to spot where a potential threat might penetrate the network. For instance, this would include how a drillship’s dynamic positioning system communicates with the rig’s BOP, how the BOP communicates with equipment on the drill floor, and how the drill floor is connected to the rig’s control system. “We want to understand, is it a one-way or two-way connection? Have we layered the network (security) between these things?” Mr Van Gemert said. “As you look at the new generation of vessels, what we’re seeing is they’re using Ethernet because it’s a lower cost way of hooking up these systems. Well, if I take Ethernet and plug it in between a BOP system and drill floor package, I create a link.” Viruses and malware can travel through this type of link, he said.
When addressing the logical systems on a rig, Mr Van Gemert said, it is important to look at what part of a rig’s configuration would be most prone to cyber threats. Often, that would include the most safety-critical systems on a rig, such as a BOP, which depends on communication between digital nodes to operate. These nodes could cease to operate due to malware infection that originates from the rig’s Ethernet connection, resulting in loss of well control. “Unless you understand the logic of how that system works, you don’t know where to address the cyber risk,” he said.
From an operational perspective, Mr Van Gemert considers the organizational philosophies a company uses to implement cybersecurity protocols amongst staff, or how the rig’s supervisors actually manage its people to mitigate cyber risks. To lessen the chance of an attack, companies should limit the number of individuals connected to the rig’s digital network to essential personnel, he said. For instance, a rig hand or third-party technician could plug into the rig’s network and unintentionally infect the system with malware. “That stays resident in these systems,” Mr Van Gemert said, unless it is intentionally removed.